Why wallet risk scoring matters (before you write a single line of code)

If you move serious value on-chain—whether you run an exchange, a custody platform, a DeFi front-end or an on‑ramp—you are already doing some sort of mental “wallet risk scoring”, even if you don’t call it that. The only difference between intuition and a real crypto wallet risk scoring software stack is that the latter is explicit, reproducible, auditable, and programmable.
In this guide, we’ll walk through a step‑by‑step blueprint for building a wallet risk score: from the history behind it, to the core concepts, to real‑world case studies, and then to the common traps that engineers and compliance teams fall into.
—
Historical background: how we got to wallet risk scores
From “follow the money” to graph analytics
Early Bitcoin investigations were mostly manual: copy‑pasting addresses into block explorers, drawing diagrams in PowerPoint, and hoping to spot patterns. Law enforcement relied on a handful of blockchain research teams that could “follow the money” using a mix of heuristics and detective work.
As volume grew, that approach broke down. Exchanges needed something always‑on, not an ad‑hoc spreadsheet. That’s where the first blockchain wallet risk assessment service providers appeared: they tagged addresses (e.g., “exchange”, “mixer”, “darknet marketplace”) and shipped dashboards and batch reports.
Soon enough, that wasn’t sufficient either. Regulators started to explicitly mention travel rules, sanctions, and FATF’s “virtual asset service providers”. Risk had to be measurable, explainable, and consistent. The solution was to convert all those tags and transaction patterns into a numerical wallet risk score that could be checked just like a credit score.
From dashboards to APIs and automation
As market structure matured, exchanges and fintechs demanded machine‑to‑machine interfaces. That’s when the modern model emerged:
– A wallet risk score API for exchanges and custodians
– Real‑time crypto transaction monitoring and risk scoring pipelines
– Embedded rules engines integrated with KYC and ticketing systems
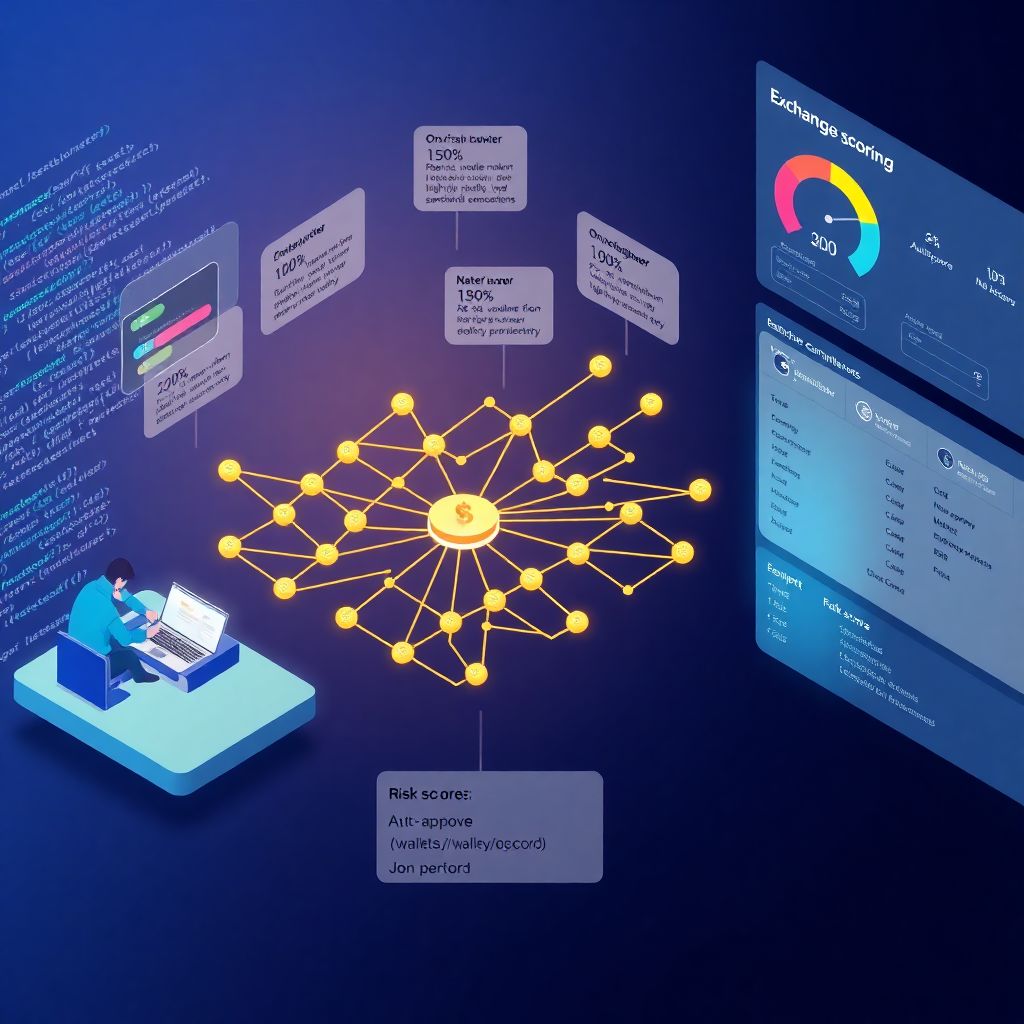
At this point, “wallet risk scoring” wasn’t a fancy add‑on. It quietly became a core layer of crypto compliance tools for wallet risk scoring, driving decisions like “auto‑approve”, “manual review”, or “block and file SAR/STR”.
—
Core ideas behind a wallet risk score
What a wallet risk score actually is
At its core, a wallet risk score is a deterministic function:
> Score = f(on‑chain behavior, off‑chain intelligence, policy parameters)
You feed in an address (or a cluster of addresses) and metadata, and the function outputs:
– A numeric score, e.g., 0–100
– A risk band, e.g., “low / medium / high”
– Explanations, like “35% of volume from high‑risk service”
The numeric value isn’t magic. It’s just a compact way to express how likely it is that interacting with this wallet could expose you to money laundering, sanctions violations, fraud, or other regulatory problems.
Short version: a wallet risk score is a compressed opinion, backed by data and rules.
The three pillars: identity, behavior, and context
Longer version: that opinion rests on three major components:
1. Identity signals
– Cluster membership (is the wallet part of a known exchange or mixer cluster?)
– Ownership hints (links to KYC’d data, leaked databases, doxxed addresses)
– Service type (gambling site, DEX, bridge, merchant, P2P broker, etc.)
2. Behavioral signals
– Flow patterns (fan‑in/fan‑out, peeling chains, mixer‑like “churn”)
– Temporal patterns (burst activity after hacks, long dormancy then big move)
– Asset mix (privacy coins, stablecoins, wrapped assets, NFTs)
3. Contextual signals
– Jurisdiction and regulatory context
– List memberships (sanctions, law‑enforcement lists, scam databases)
– Counterparty risk (who this wallet tends to talk to)
A robust crypto wallet risk scoring software stack exposes these pillars instead of hiding everything behind a single “magic number”.
—
Step‑by‑step guide: from raw chain data to usable scores
Step 1: Define the risk you actually care about
Before writing code, you need a risk taxonomy. “Bad wallet” is too vague.
For a typical exchange, distinct buckets might include:
1. Sanctions and embargoed entities
2. Terrorist financing and organized crime
3. Fraud and scams (investment fraud, romance scams, phishing)
4. Illicit services (darknet markets, unlicensed gambling, illegal casinos)
5. Regulatory exposure (unlicensed money transmission, travel rule issues)
Each bucket can map to a specific dimension in your scoring model. For instance, you might track a “sanctions risk sub‑score” separately from a “fraud exposure sub‑score”.
Short but important: if you don’t define categories, your score will be hard to defend when an auditor asks “what does 82 actually mean?”.
Step 2: Build or choose your data ingestion pipeline
Next, you need transaction data and labels. There are three broad strategies.
1. Use a third‑party blockchain wallet risk assessment service
You call a SaaS provider’s API; they handle enrichment, clustering, and tagging.
Pros: Fast to market.
Cons: Cost, opacity, vendor risk.
2. Self‑hosted node + enrichment
– Run archive or full nodes for the chains you care about
– Index blocks, transactions, logs, and traces
– Store normalized data in a time‑series or graph‑oriented database
3. Hybrid
– Core indexing in‑house
– Labels and intelligence (e.g., hack lists, sanctions tags) from vendors
Whatever you pick, make sure your architecture can support low‑latency lookups; otherwise, real‑time crypto transaction monitoring and risk scoring will be painful.
Step 3: Design your labeling and clustering strategy
You can’t score what you don’t recognize.
1. Entity clustering
– Heuristics: common‑input ownership (for UTXO chains), multi‑sig patterns, change address detection
– Empirical labels: deposit addresses published by exchanges, on‑chain proofs, public statements
2. Service classification
For each cluster, try to classify:
– Exchange, CEX hot wallet, broker
– Mixer / tumbler / privacy pool
– DeFi protocol (DEX, lending, staking, bridge)
– Merchant, NGO, charity, OTC desk, etc.
3. Risk tagging
– High‑risk: mixers, sanctioned entities, hacked funds, major scam clusters
– Medium‑risk: unlicensed exchanges, offshore casinos, some P2P brokers
– Low‑risk: regulated exchanges, large payment processors, reputable custodians
This is where crypto compliance tools for wallet risk scoring differ in quality: better tools don’t just have more tags; they have better‑curated, continuously updated tags, plus lineage history (since when and why something is tagged).
Step 4: Define your scoring model

Now you translate data into numbers. There are two main approaches, often combined.
1. Rule‑based (deterministic) scoring
Example structure:
– Start at base score = 0
– Add +40 if direct counterparty is on a sanctions list
– Add +25 if >30% of volume from mixers in last 30 days
– Add +15 if volume spike >10× baseline occurred in last 24 hours
– Cap at 100
This is easy to explain to regulators and auditors.
2. Statistical or ML‑assisted scoring
– Engineer features (in/out degree, flow centrality, time‑between‑tx, entropy of counterparties, lifetime turnover)
– Train models (gradient boosting, random forest, graph neural networks) to predict “suspicious vs not” based on historical alerts or confirmed cases
– Translate model outputs (probabilities) into calibrated scores and bands
A pragmatic pattern: use rules for “hard” constraints (e.g., OFAC = auto max score), and ML to refine the “grey zone” where patterns are subtle.
Step 5: Implement exposure calculations
One of the biggest nuances in wallet risk scoring is indirect exposure. It’s not only about whether a wallet directly touched a bad actor, but also *how far removed* it is.
For example:
1. Direct exposure – wallet received funds straight from a sanctioned address.
2. One‑hop exposure – wallet received from someone who got funds from a sanctioned address.
3. Multi‑hop exposure with decay – risk decreases with each hop, often using an exponential decay function.
A common approach is:
– Define maximum hop depth (e.g., 3–4 hops)
– Apply decay factor per hop (e.g., 0.5^n)
– Aggregate weighted risk contributions from all relevant ancestors
Your risk engine should also compute proportional exposure: if only 5% of a wallet’s inflows trace back to high‑risk sources, that’s very different from 95%. This is where modern crypto transaction monitoring and risk scoring pipelines lean heavily on graph databases and optimized traversal algorithms.
Step 6: Calibrate and test your score
You now have a working score, but not a reliable one until you calibrate it.
1. Backtest against historical incidents
– Known hacks
– Seized darknet funds
– Confirmed scam rings
Check: did your model assign high scores to those wallets before they were publicly announced?
2. Compare across risk bands
– Are “high‑risk” wallets really more often involved in alerts and SARs?
– Are you flooding your compliance team with false positives?
3. Set operational thresholds
Example:
– Score 0–29: auto‑approve
– 30–59: allow but log / soft‑monitor
– 60–79: flag for manual review
– 80–100: block, escalate, consider filing SAR/STR
This is also where feedback from human investigators loops back into your scoring: each confirmed case should improve future scoring, even in a mostly rule‑based system.
Step 7: Ship an API and integrate it
A scoring engine isn’t useful until other systems can call it. Typical design:
– REST or gRPC API with endpoints like `/wallets/{address}/risk_score`
– Optional bulk endpoints for batch jobs
– Response should contain:
– Score and band
– Breakdown by risk category
– Top reasons / contributing factors
For production‑grade usage, the wallet risk score API for exchanges will usually sit in front of a cache. Hot wallets and frequent counterparties will hit the cache; cold or new addresses will go to the engine and then be cached.
Finally, hook this into your:
– Withdrawal / deposit flows
– Case management tools
– Alerting / ticketing systems
– Reporting stack for regulators and internal stakeholders
—
Real‑world cases: what wallet risk scoring looks like in practice
Case 1: Mid‑size exchange stops a sanctions breach
A European mid‑size exchange integrated a third‑party blockchain wallet risk assessment service but initially used it only as a manual tool: analysts would paste in suspicious addresses when they had time.
They then implemented automated scoring for every deposit address:
1. New inbound deposit arrives.
2. System calls the risk scoring API with the sending address.
3. Score comes back at 93/100 with reason:
– Direct 1‑hop exposure to sanctioned entity
– >60% of last month’s volume from high‑risk mixer cluster
Previously, this deposit would likely have been auto‑credited. With the new pipeline:
– Deposit is immediately frozen
– Automated ticket created in the AML system
– Investigation confirms: funds trace back to a recently designated Russian entity
The exchange files a report with the relevant FIU and updates its internal block list. The key insight: the actual code change was small (an extra API call), but the design of the wallet risk score and response workflow prevented a serious regulatory violation.
Case 2: DeFi front‑end adds a “soft guardrail”
A popular DeFi aggregator didn’t want to block transactions outright but wanted to warn users when they might be touching risky funds.
They built a lightweight internal risk engine:
1. Indexed swaps and transfers for a few major EVM chains.
2. Created a coarse‑grained tag set: “known hack”, “mixer”, “large CEX”, “DEX pool”.
3. Implemented a simple rule:
– If any counterparty pool or wallet has >50% of its liquidity linked to “known hack” tags, flag it as “high‑risk”.
When a user tried to route through a flagged pool, the UI would display:
> “Heads up: this pool has significant exposure to wallets associated with prior hacks. Proceed only if you understand the risk.”
This wasn’t about regulatory compliance as much as user protection and reputational risk. Their approach shows that wallet risk scoring doesn’t have to be heavy or centralized; you can deploy thin, targeted logic close to the user.
Case 3: Neobank discovers a false‑positive factory
A regulated neobank offering crypto accounts integrated a turnkey crypto wallet risk scoring software platform and set a strict policy:
– Any inbound transfer with score ≥ 70 gets auto‑blocked pending review.
Within days, their support queues exploded. Users were angry: “Why are my withdrawals from Exchange X blocked? They are fully licensed!”
After investigation, they learned:
– The vendor classified a cluster of addresses as “unregulated exchange” based on old intelligence.
– That cluster had since been acquired and properly licensed, but the tags weren’t updated.
– A big chunk of the neobank’s user base used that exchange, so every transfer was scoring 75–80.
Fix:
1. The bank forced the vendor to update labels and add freshness metadata.
2. They moved from a single vendor to a multi‑source model.
3. Internally, they added a “trusted partner” override that reduced risk scores for vetted counterparties.
This case highlights how over‑reliance on opaque third‑party scoring can create systemic false positives—and why explainability and data provenance matter as much as the score itself.
—
Frequent misconceptions and how to avoid them
Misconception 1: “One score number is enough”
Many teams try to collapse everything into a single number and treat it as absolute truth. That makes dashboards look neat but creates problems:
– Hard to explain why a specific wallet scored 78 vs 62
– Difficult to tune policy for different risk categories
– Almost impossible to debug anomalous results
A better approach is to keep sub‑scores (e.g., sanctions risk, fraud risk, mixer exposure) and then derive a composite score. Compliance can then craft clearer rules, like:
1. If sanctions sub‑score > 80 → auto block.
2. If fraud sub‑score > 60 but sanctions < 20 → manual review, not immediate block.
Short rule of thumb: a wallet risk score without decomposition is a black box—and regulators don’t like black boxes.
Misconception 2: “On‑chain is all that matters”
On‑chain behavior is powerful, but it’s not the whole picture. Some risk patterns live mostly off‑chain:
– Phishing sites collecting seed phrases
– Social‑engineering scams recruiting victims in chat apps
– Coordinated rings of mules that use fresh addresses each time
Your scoring logic should integrate:
– Case management outputs (which addresses investigators confirm as scams)
– External threat feeds and law‑enforcement notices
– Customer KYC data (where legally allowed and technically appropriate)
Think of on‑chain analytics as a strong base layer; you still need higher layers tied to user identity and external intelligence to build a complete risk assessment.
Misconception 3: “ML will solve everything magically”
Machine learning can absolutely improve detection, but only if:
– Features are well‑engineered and grounded in domain knowledge
– Labels are trustworthy (you’re not training on a pile of noisy, biased “suspect” flags)
– You have a feedback loop to correct drift and weird behavior
In practice, many teams ship black‑box models without interpretability, which backfires when a regulator asks, “Explain why this user was blocked.” For critical decisions—especially those with customer impact—keep a transparent rule layer and use ML as a decision support tool, not the sole source of truth.
Misconception 4: “Vendor = solved problem”
Integrating a third‑party blockchain wallet risk assessment service or other crypto compliance tools for wallet risk scoring reduces engineering effort, but doesn’t eliminate responsibility. You still own:
– Policy design (what scores map to which actions)
– Calibration and threshold selection
– Periodic vendor validation and benchmarking
– Documentation and justification to regulators
You can outsource plumbing, labels, and even models, but you can’t outsource accountability.
—
Putting it all together
A solid wallet risk score system is not just an API call; it’s an ecosystem:
1. Clear definition of what “risk” means for your business and regulators.
2. Reliable data ingestion, enrichment, clustering, and tagging.
3. A transparent, tunable scoring model combining rules and analytics.
4. Exposure logic that accounts for graph structure and decay.
5. Calibration, backtesting, and continuous feedback from human investigators.
6. Production integration through fast, well‑designed APIs and workflows.
If you design with these principles in mind, you’ll end up with more than a numeric score—you’ll have a defensible, explainable, and adaptable framework that can grow alongside the evolving crypto ecosystem.